How to Achieve PCI DSS Compliance for Azure Virtual Machines
How to Achieve PCI DSS Compliance for Azure Virtual Machines
PCI DSS compliance is critical to protecting cardholder data that is processed, stored, and transmitted. Pulumi can assist you with making your Azure infrastructure PCI DSS compliant. Pulumi can help you identify existing cloud resources that are not in compliance, and it can also enforce compliance policies proactively before infrastructure is deployed. Get started with Pulumi to use these compliance tools or speak with a Solutions Architect to get an expert consultation.
What is PCI DSS Compliance?
PCI DSS (Payment Card Industry Data Security Standard) compliance refers to the adherence to a set of security standards designed to protect card information during and after a financial transaction. These standards are established by the Payment Card Industry Security Standards Council (PCI SSC), which was founded by major credit card companies like Visa, MasterCard, American Express, Discover, and JCB.
Key Aspects of PCI DSS Compliance
- Security Controls: Organizations must implement specific technical and operational security measures to safeguard cardholder data. This includes requirements like installing firewalls, encrypting cardholder data, and using antivirus software.
- Access Control: Only authorized personnel should have access to cardholder data. This involves setting up strong access control measures, such as unique user IDs and restricting physical access to sensitive data.
- Monitoring and Testing: Regularly monitor and test networks to ensure that security controls are functioning correctly and to identify vulnerabilities. This includes maintaining logs of all access to network resources and cardholder data.
- Information Security Policy: Organizations must maintain a policy that addresses information security for employees and contractors. This includes regular security awareness training.
- Regular Audits: Organizations that process, store, or transmit credit card information must undergo regular audits to ensure they are in compliance with PCI DSS requirements. This can involve self-assessment or external assessments, depending on the size of the organization and the volume of transactions processed.
Pulumi Insights
Use Pulumi Insights to gain visibility into your cloud infrastructure's configuration to assess PCI DSS compliance. Pulumi Insights is Intelligent Cloud Management. It helps you gain security, compliance, and cost insights into the entirety of your organization's cloud assets and automatically remediate issues.
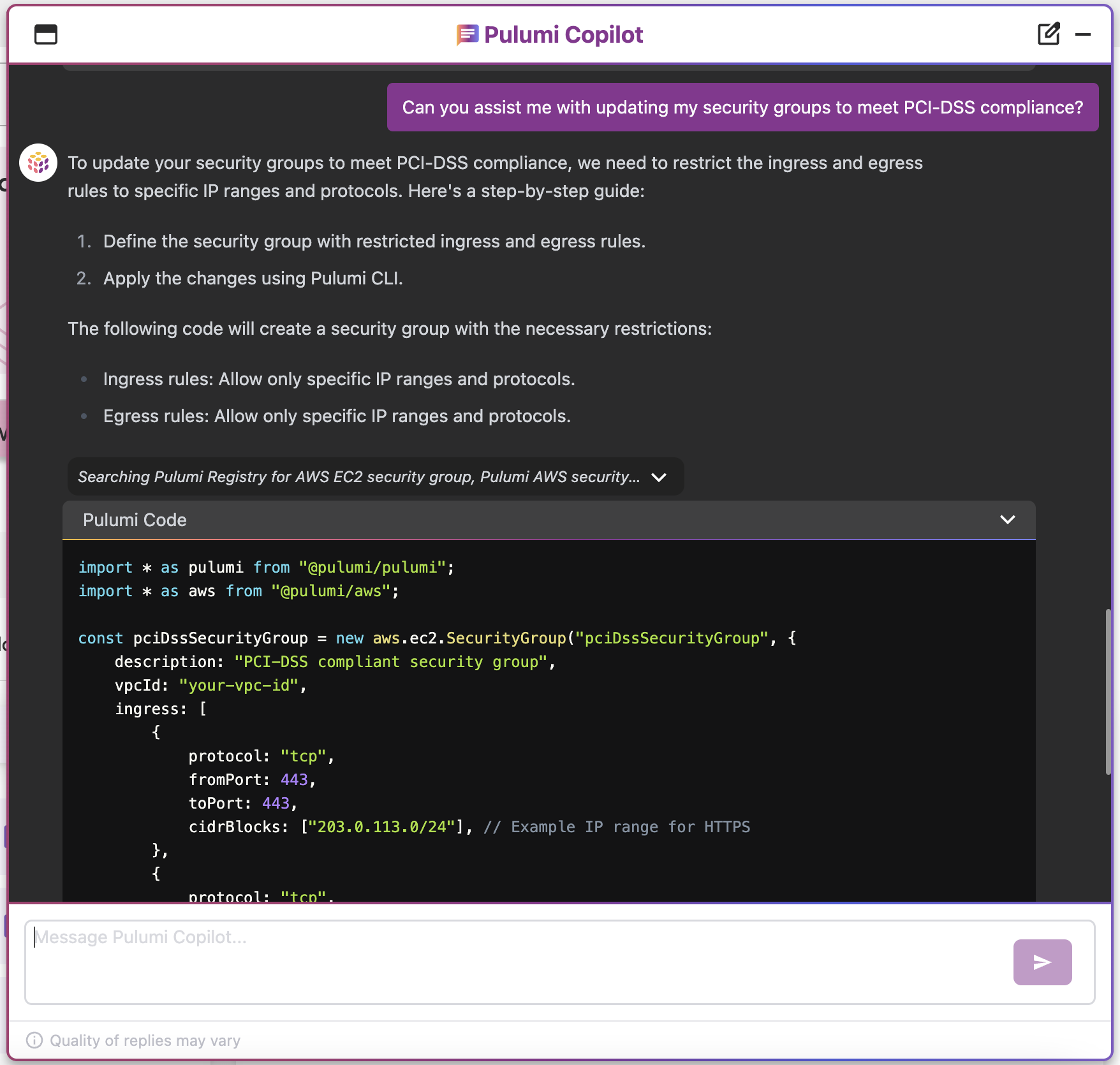
Pulumi Copilot
Use Pulumi Copilot to assist configuring your infrastructure to make it compliance ready. You can tap into the Pulumi Copilot's deep understanding of your organization's context to gain visibility into the configuration of resources and assess their compliance.
Compliance Ready Policies
With comprehensive coverage of Azure, Pulumi Compliance Ready Policies provide an enhanced level of control and governance over your cloud resources. Pulumi Compliance Ready Policies empower you to enforce best practices, security standards, cost controls, and compliance requirements seamlessly within your infrastructure-as-code workflows.
What is Azure Virtual Machines?
Azure Virtual Machines provide scalable, on-demand compute resources in the cloud, enabling users to run applications, deploy workloads, and manage operating systems without maintaining physical hardware. With support for various operating systems like Windows and Linux, users can configure and scale VMs to meet their performance and cost requirements. Azure Virtual Machines offer features like auto-scaling, high availability, and seamless integration with other Azure services for enhanced cloud-based computing.
What controls can I put in place to evaluate Azure Virtual Machines resources?
- Azure Managed Disks snapshots should not be publicly restorable
- Azure Virtual Network (VNet) default network security groups (NSGs) should not allow inbound or outbound traffic
- Attached Azure Managed Disks should be encrypted at rest
- Stopped Azure Virtual Machines (VMs) should be removed after a specified time period
- Network security logging should be enabled for all Azure VNets
- Default encryption for Azure Managed Disks should be enabled
- Azure VMs should use Instance Metadata Service Version 2 (IMDSv2)
- Azure Virtual Machines should not have a public IP address
- Azure Virtual Machines should be configured to use private link or VNet service endpoints
- Unused Azure Public IPs should be removed
- Network security groups should not allow ingress from 0.0.0.0/0 to SSH port (22)
- Network security groups should not allow ingress from 0.0.0.0/0 to RDP port (3389)
- Azure Virtual Networks should not automatically assign public IP addresses
- Unused Network Security Groups should be removed
- Azure Virtual Machines should not use multiple network interfaces (NICs)
- Network security groups should only allow unrestricted incoming traffic for authorized ports
- Network security groups should not allow unrestricted access to high-risk ports
- Both VPN tunnels for an Azure VPN Gateway connection should be up
- Network security groups should not allow ingress from 0.0.0.0/0 to port 22 or port 3389
- Azure Virtual Network (VNet) peering connections should not automatically accept peering requests
- Azure VM instances should not use legacy VM types
- Azure VM scale sets should not assign public IPs to NICs
- Azure Managed Disks should be covered by a backup policy
- Azure Virtual Network Gateway connections should be tagged
- Azure Virtual Network route tables should be tagged
- Azure Network Interfaces (NICs) should be tagged
- Azure Virtual Network Gateways should be tagged
- Azure Public IPs should be tagged
- Azure Virtual Machines should be tagged
- Azure Virtual Network Gateways should be tagged
- Azure NAT Gateways should be tagged
- Azure Network Security Groups should be tagged
- Azure Virtual Networks should be tagged
- Azure Virtual Network endpoint services should be tagged
- Azure VNet flow logs should be tagged
- Azure VNet peering connections should be tagged
- Azure VPN Gateways should be tagged
- Azure Client VPN endpoints should have client connection logging enabled
- Azure Virtual Network Gateways should be tagged
Speak to a Solutions Architect to implement policy as code to manage Virtual Machines resources for PCI DSS compliance.
Talk to a Solutions Architect
Get in touch with our Solutions Architects to get all your resources in use with Pulumi Insights